It’s been awhile since I’ve been in the Alta ecosystem, I was one of the early adopters of the AP6 and wanted to get back into the Alta ecosystem. Anyway, I just ordered the Alta route 10 and I’m curious what speeds anyone using the Wireguard VPN client out to a service like Surfshark or Mulvad are seeing?
I haven’t tried it out much but running speedtest and bufferbloat right now using SurfShark is that speed is not affected much at all given my nominal speed 630/630, or with CAKE tuning which limits output to 570/570. Latencies are affected but still fairly low. Nominal ~15/+8/+10, with CAKE ~15/+2/+6, CAKE+SurfShark ~16/+7/+15.
I don’t know if these numbers are sensible but I guess it is reasonable to suspect that CAKE can’t handle tunneled data fully.
Any other similar or contradictory experiences?!
This is perfect, thanks! I’m currently using the GL.Inet Flint 3 I got from them as part of a beta test. I’m getting around ~400-500mbps with that on a 1gig plan. I was looking for something with a little bit better performance and the Route 10 looks to be it. I use a VPN client on my network because of work and also privacy/ad blocking.
1 more question, does it allow you do disable or exclude 1 device from the VPN client? Like a chromecast?
I have to admit I am not entirely sure that the SurfShark tunnel is properly up and running. So I can’t vouch for the numbers yet. There might be something wrong with the either the export from SurfShark and/or import to Route10, because I can’t see any public IP change (as I would expect from the masquerade option?!) or any additional hops from a trace route to for example Google/8.8.8.8). I’ll try to verify it is up and running or, if not, try to make it so and get back.
Edit: Now I recall that I actually didn’t get the UI way of configuring the SurfShark tunnel working. However, I somehow managed it via CLI, but I have to dig up the scripts for that. See previous threads:
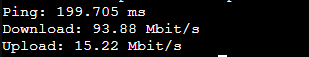
This is my speed for mullvad. I pay for 500down 20 up through spectrum so not too bad for routing to sweden from the US.
Getting back to this one. I believe I have finally managed to perform a scripted setup of a Surfshark-client. At the Route10 level I get a 4-5 % performance loss through the closest VPN server.
Here’s the result from an automated speedtest comparison for test through WAN interface and surfshark interface, respectively.
================ Surfshark VPN Test ================
🔲 Checking public IPs...
✅ Public IP through Surfshark: 185.76.9.56
✅ Surfshark IP is different from WAN IP (hidden)
🔲 Running baseline speedtest (direct WAN)...
✅ Baseline download: 571.24 Mbps, upload: 578.26 Mbps, ping: 5.571 ms
🔲 Running Surfshark VPN speedtest through wgSurfshark...
✅ Surfshark download: 546.54 Mbps, upload: 548.48 Mbps, ping: 6.274 ms
================== Summary ==================
Direct WAN : ↓ 571.24 Mbps | ↑ 578.26 Mbps | ping 5.571 ms
Surfshark : ↓ 546.54 Mbps | ↑ 548.48 Mbps | ping 6.274 ms
Download loss through Surfshark: 4.3%
Upload loss through Surfshark: 5.1%
Latency difference: +0.7 ms
=============================================
# ✅ = passed, ⚠️ = needs attention, ❌ = failed
The nominal speed is 630 up/down, then reduced to appr. 570-580 by enabling CAKE with tuning optimized for my setup. Then another drop to around 540-550 through the Surfshark VPN-tunnel. Very good indeed.
Edit: Following up with some data from a WiFi client (Android device), where I got 500-550 down and 450-550 up. Bufferbloat grade A for Surfshark vs. A+ for nominal with CAKE.
Could you share your script?
A few iterations with the help of AI. Shout out if you spot any issues with it.
Interface name is hardcoded. Speedtest must be installed.
#!/bin/sh
#
# /cfg/scripts/test-surfshark.sh
# ------------------------------------------------
# Compare Surfshark vs direct WAN speeds (no bc)
# Shows % difference for download, upload, latency
# Also checks that Surfshark IP != WAN IP (hidden)
#
IFACE="wgSurfshark" # Surfshark WireGuard interface
checkbox () { # usage: checkbox "label" "OK|WARN|FAIL"
case "$2" in
OK) echo "✅ $1";;
WARN) echo "⚠️ $1";;
FAIL) echo "❌ $1";;
*) echo "🔲 $1";;
esac
}
to_mbps () { # bytes/sec -> Mbps
val="${1:-0}"
awk "BEGIN {printf \"%.2f\", $val/125000}"
}
extract_download () { # JSON -> download.bandwidth (bytes/sec)
sed -n 's/.*"download":{[^}]*"bandwidth":\([0-9]\+\).*/\1/p'
}
extract_upload () { # JSON -> upload.bandwidth (bytes/sec)
sed -n 's/.*"upload":{[^}]*"bandwidth":\([0-9]\+\).*/\1/p'
}
extract_latency () { # JSON -> ping.latency (ms)
sed -n 's/.*"latency":\([0-9.]\+\).*/\1/p'
}
percent_diff () { # base, vpn -> prints % loss (positive) or % gain (negative)
base="$1"
vpn="$2"
awk "BEGIN {
if ($base > 0) printf \"%.1f\", 100 - ($vpn/$base*100)
else print \"0.0\"
}"
}
echo "================ Surfshark VPN Test ================"
echo
# 1) Check WAN IP vs Surfshark IP
echo "🔲 Checking public IPs..."
WANIP=$(curl -s https://ifconfig.io)
VPNIP=$(curl -s --interface "$IFACE" https://ifconfig.io)
if [ -n "$VPNIP" ]; then
checkbox "Public IP through Surfshark: $VPNIP" OK
else
checkbox "Could not get public IP through $IFACE" FAIL
fi
if [ -n "$WANIP" ] && [ -n "$VPNIP" ]; then
if [ "$WANIP" != "$VPNIP" ]; then
checkbox "Surfshark IP is different from WAN IP (hidden)" OK
else
checkbox "Surfshark IP appears SAME as WAN IP (VPN not working?)" WARN
fi
fi
echo
# 2) Baseline (direct WAN) speedtest
echo "🔲 Running baseline speedtest (direct WAN)..."
BASE_JSON=$(speedtest --format=json 2>/dev/null)
BASE_DOWN_BPS=$(echo "$BASE_JSON" | extract_download)
BASE_UP_BPS=$(echo "$BASE_JSON" | extract_upload)
BASE_PING=$(echo "$BASE_JSON" | extract_latency)
BASE_DOWN_MBPS=$(to_mbps "$BASE_DOWN_BPS")
BASE_UP_MBPS=$(to_mbps "$BASE_UP_BPS")
checkbox "Baseline download: $BASE_DOWN_MBPS Mbps, upload: $BASE_UP_MBPS
Mbps, ping: ${BASE_PING:-?} ms" OK
echo
# 3) Surfshark (VPN) speedtest
echo "🔲 Running Surfshark VPN speedtest through $IFACE..."
VPN_JSON=$(speedtest -I "$IFACE" --format=json 2>/dev/null)
VPN_DOWN_BPS=$(echo "$VPN_JSON" | extract_download)
VPN_UP_BPS=$(echo "$VPN_JSON" | extract_upload)
VPN_PING=$(echo "$VPN_JSON" | extract_latency)
VPN_DOWN_MBPS=$(to_mbps "$VPN_DOWN_BPS")
VPN_UP_MBPS=$(to_mbps "$VPN_UP_BPS")
checkbox "Surfshark download: $VPN_DOWN_MBPS Mbps, upload: $VPN_UP_MBPS Mbps, ping: ${VPN_PING:-?} ms" OK
echo
# 4) Performance summary
echo "================== Summary =================="
echo "Direct WAN : ↓ $BASE_DOWN_MBPS Mbps | ↑ $BASE_UP_MBPS Mbps | ping ${BASE_PING:-?} ms"
echo "Surfshark : ↓ $VPN_DOWN_MBPS Mbps | ↑ $VPN_UP_MBPS Mbps | ping ${VPN_PING:-?} ms"
if [ "$BASE_DOWN_BPS" -gt 0 ] && [ "$VPN_DOWN_BPS" -gt 0 ]; then
LOSS_DOWN=$(percent_diff "$BASE_DOWN_BPS" "$VPN_DOWN_BPS")
LOSS_UP=$(percent_diff "$BASE_UP_BPS" "$VPN_UP_BPS")
LAT_DIFF=$(awk "BEGIN {printf \"%.1f\", (${VPN_PING:-0}-${BASE_PING:-0})}")
echo
echo "Download loss through Surfshark: ${LOSS_DOWN}%"
echo "Upload loss through Surfshark: ${LOSS_UP}%"
echo "Latency difference: +${LAT_DIFF} ms"
fi
echo "============================================="
echo "# ✅ = passed, ⚠️ = needs attention, ❌ = failed"