Another suggestion for improvement of IDS/IPS.
I have found it not so straightforward to understand if events in the IDS/IPS Events log are related to drop/block or info/alert “type” of actions.
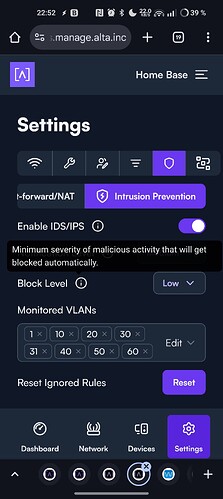
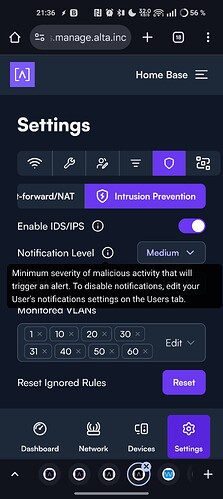
The configuration of IDS/IPS says “Minimum severity of malicious activity that will be blocked automatically”. I suspect that is not entirely true as a lot of alerts that gets logged in the events list are actually not associated to activity that gets blocked but rather only informed/alerted upon.
I know that there is probably a lot of Suricata documentation on the respective rules that gets triggered, but would it be possible to add some more basic info on the distinction between dropped traffic versus information only in the Events log?