Hi Matt
I have recently configured the Route 10 router but do not have any Alta AP’s, does that mean I cannot block a device as I do not see the cross icon rather just a delete icon.
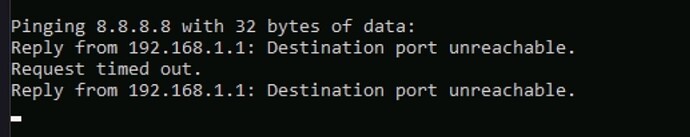
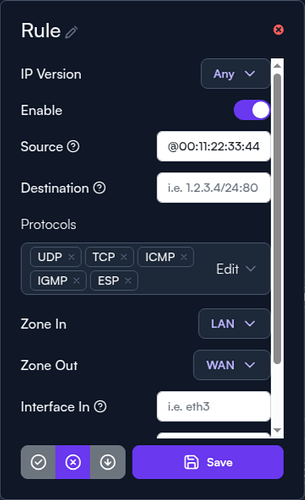
I created a firewall rule to drop traffic to the specific device based on IP but it doesn’t do the job, some of the features still run and only way I can do is to have the DL/UL speed set to very very low like 0.00001
Any help would be appreciated
Thanks
Hi @binodnepal and welcome to the community!
That’s correct. Right now, there is no wired blocking like you would normally see for wireless devices. This is something actively being worked on.
But this doesn’t mean you’re out of luck. You should be able to block via firewall rules. If you can share a screenshot of the rule(s) you created that aren’t working, we should be able to correct them to block traffic.
Additionally, you could override any number of settings for the client(s) in the Devices tab; the first one that comes to mind is to override the VLAN to one that doesn’t exist.
Hi Matt
Thank you so much for the reply.
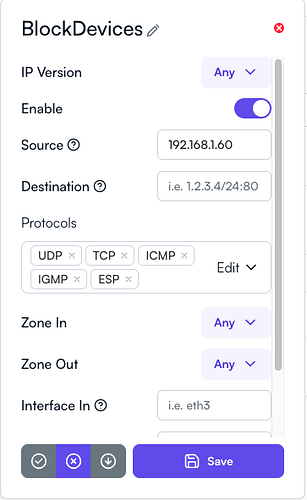
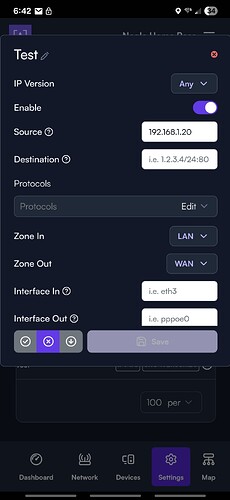
Please check the screenshot, One more thing while changing the settings on an individual device it keeps on popping up saying multiple device will be affected so it just make it so confusing, like,
am I changing only for the selected device or will it affect others too.
thanks
Binod
Thanks DN,
I will give it a try
it is working, thanks heaps
Good to know! My devices that are blocked are static though I will probably use this method going forward.
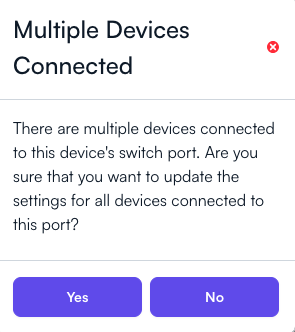
I initially had the same opinion. However, I’ve come to find that this warning is very crucial if you’re running mixed vendor networks (which is often the root of why you’ll see the warning in the first place). If you’re making interface changes on a port that is upstream for another vendor’s switch, the outcome may not be what you’re expecting. It’s simply a stop gap if there are more than 1 MAC address detected downstream of the relevant change you’re making.
I would agree if the change had an interface specified. The warning is saying you are updating the settings for all devices connected to this port which doesn’t make sense in this case. No port is being specified, it’s a single ip, which I think is where the confusion comes from when people get that warning. I know I hesitated when I got it the first time and tried to make sense of it but had to come to the forum to find the answer. Ultimately, I don’t think it’s that big of a deal, the language chosen is just confusing when the changes you are making dont reflect what its warning you about.
Hi Matt
I tried assigning a VLAN that doesn’t exist, e.g. 2 and it I thought it was only supposed to change this device, rather what it did was it changed the VLAN of my unifi AP that the device was connecting to it and brought the whole network down. Why will this happen, does it go and change the VLAN for the physical port that the unifi ap was connected to, I am puzzled with this VLAN on device setting.
Any help is appreciated.
Thanks
Binod
Is the device in question associated to the UniFi AP or the Alta AP?
I am changing the VLAN on one of the iPad, it did change the VLAN but also changed the VLAN for the AP the iPad was connected too, doesn’t that should only change the device I am changing the VLAN for, in this case just the iPad, thanks
I will double check, but my current understanding is, if that device were connected to an Alta AP, the VLAN change would occur on the AP itself. Since it’s not connected to an Alta AP, it gets applied to the closest network device, which seems to be a UniFi AP. I believe that you’ve hit a circumstance where that “Multiple Devices Connected” warning is a legitimate purpose, but I will confirm my understanding of the function.
I did get the warning but doesn’t it supposed to just modify the device I am interested in rather than where it is connected to.
Thanks
The device you are connected to has no support or understanding of VLANs; client devices typically do not tag or untag VLANs on their own network interfaces, instead relying on the upstream network device to manage the VLAN on its behalf. As a result, device-level VLAN configurations must be applied to the network devices that we have management access on. For wireless clients, that is going to be on the AP first, where we could apply a new default network VLAN or possibly a VLAN to the AltaPass which the client is connected to.
In your situation, as I understand, you don’t have an Alta AP in place for this client device. We cannot manage the configuration of your third-party access point, so the setting must move further upstream to our switch. The result is that the physical interface in which the third-party AP is connected will then be configured with the Native VLAN you chose. This means our switch will adopt this VID on the port that AP is plugged into, which will of course affect every device connected downstream of that port – the AP and all of its wireless clients.
You can manage the VID associated through their controller or configuration page instead, if you need to narrow its application further.