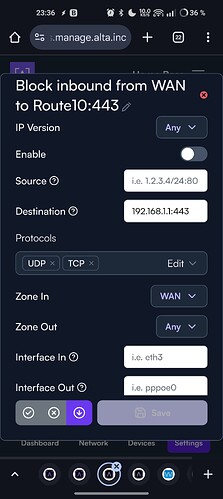
How exactly do you access control the management services such as TCP 80/443/22 on the Route10 Product WAN interfaces?
I would like to reduce the attack surface of listening ports on the appliance:
~ # netstat -tulpn
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:80 0.0.0.0:* LISTEN 8138/uhttpd
tcp 0 0 127.0.0.1:53 0.0.0.0:* LISTEN 5612/dnsmasq
tcp 0 0 192.168.1.1:53 0.0.0.0:* LISTEN 5612/dnsmasq
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 5923/dropbear
tcp 0 0 0.0.0.0:443 0.0.0.0:* LISTEN 8138/uhttpd
tcp 0 0 :::80 :::* LISTEN 8138/uhttpd
tcp 0 0 fe80::beb9:23ff:fe81:8d01:53 :::* LISTEN 5612/dnsmasq
tcp 0 0 fe80::beb9:23ff:fe81:8d00:53 :::* LISTEN 5612/dnsmasq
tcp 0 0 ::1:53 :::* LISTEN 5612/dnsmasq
tcp 0 0 :::22 :::* LISTEN 5923/dropbear
tcp 0 0 :::443 :::* LISTEN 8138/uhttpd
udp 0 0 0.0.0.0:1701 0.0.0.0:* 6543/xl2tpd
udp 0 0 0.0.0.0:5353 0.0.0.0:* 7053/rc
udp 0 0 127.0.0.1:5053 0.0.0.0:* 32140/https-dns-pro
udp 0 0 127.0.0.1:5054 0.0.0.0:* 32139/https-dns-pro
udp 0 0 127.0.0.1:5055 0.0.0.0:* 32141/https-dns-pro
udp 0 0 192.168.70.5:53 0.0.0.0:* 5612/dnsmasq
udp 0 0 127.0.0.1:53 0.0.0.0:* 5612/dnsmasq
udp 0 0 192.168.1.1:53 0.0.0.0:* 5612/dnsmasq
udp 0 0 0.0.0.0:67 0.0.0.0:* 5612/dnsmasq
udp 0 0 :::547 :::* 5612/dnsmasq
udp 0 0 fe80::beb9:23ff:fe81:8d01:53 :::* 5612/dnsmasq
udp 0 0 fe80::beb9:23ff:fe81:8d00:53 :::* 5612/dnsmasq
udp 0 0 ::1:53 :::* 5612/dnsmasq